[Archived] AWS IAM Identity Center
Last updated: December 9, 2025
This article applies only to AWS connections created before July 2025. To check which version you’re using, look at the Domain ID under your domain:
If the domain name shows
aws.amazon.com, continue with the steps below.
If it shows
aws-sso_ics, proceed with instructions in this article.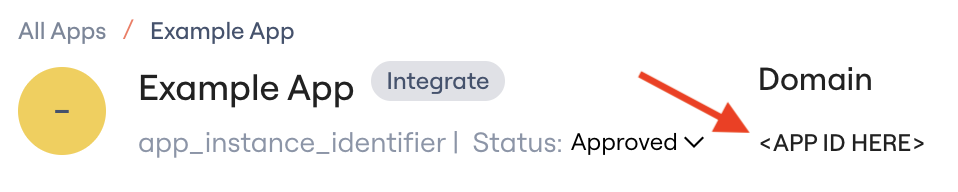
Lumos integrates with AWS IAM Identity Center to help you conduct access reviews across your AWS accounts. We surface IAM Identity Center users, the accounts they can access, and their permission sets. If SCIM is enabled, Lumos also supports automated user deprovisioning or suspension.
Prerequisites
You must have elevated AWS permissions for:
IAM
IAM Identity Center (SSO)
AWS Organizations
Connection Instructions
Step 1: Enable SCIM and Collect Required Values
Go to the IAM Identity Center console → Settings.
Confirm Identity source shows as External identity provider.
If not, follow these instructions.
Click Actions → Manage Provisioning:
Copy the SCIM endpoint value to the
Tenant IDfield (e.g.,Nvdk4lx216-7d1e-4759-f84a-047fj48sd370).Click Generate token → copy to the
API Keyfield.
Back on the Settings page:
Copy the IAM Identity Center ARN.
Find your AWS Region (top-right corner near your email, e.g.,
us-west-2).
Step 2: Create IAM Role for Lumos
You can create the role via AWS Console or Terraform.
Option A: AWS Console
IAM Console → Roles → Create Role.
Select Another AWS account → enter Account ID
349123981986.Enable Require external ID and enter a secure value.
Add permissions:
For simplest management, attach:
AWSSSODirectoryAdministratorAWSSSOMasterAccountAdministrator
For least privilege, use this custom policy:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "AllowAccessToIdentityCenter",
"Effect": "Allow",
"Action": [
"identitystore:ListUsers",
"identitystore:ListGroupMemberships",
“identitystore:DescribeUser”,
“identitystore:ListGroups”,
“identitystore:DescribeGroup”,
"identitystore:GetGroupMembershipId"
"identitystore:CreateUser",
"identitystore:DeleteUser",
"organizations:DescribeAccount",
"organizations:ListAccounts",
"sso:DescribePermissionSet",
"sso:ListPermissionSets",
"sso:ListAccountAssignments",
"sso:ListAccountsForProvisionedPermissionSet",
“sso:ListPermissionSetsProvisionedToAccount”,
"sso:ListInstances",
"sso:ListPermissionSets",
"sso:DescribeInstance",
"sso:DeleteAccountAssignment",
"sso:CreateAccountAssignment"
],
"Resource": "*"
},
{
"Sid": "AccessToSSOProvisionedRoles",
"Effect": "Allow",
"Action": [
"iam:AttachRolePolicy",
"iam:DeleteRolePolicy",
"iam:DetachRolePolicy",
"iam:ListAttachedRolePolicies",
"iam:GetRole",
"iam:CreateRole",
"iam:DeleteRole",
"iam:PutRolePolicy",
"iam:UpdateRole",
"iam:ListRolePolicies",
"iam:UpdateRoleDescription",
“iam:GetSAMLProvider",
],
"Resource": "arn:aws:iam::*:role/aws-reserved/sso.amazonaws.com/*"
},
{
"Sid": "AccessToSCIMProvider",
"Effect": "Allow",
"Action": [
"iam:GetSAMLProvider"
],
"Resource": "arn:aws:iam::*:saml-provider/AWSSSO_*_DO_NOT_DELETE"
}
]
}
Edit the trust relationship:
Set
Principalto:arn:aws:iam::349123981986:user/global-service-account
Set Max session duration to 12 hours.
Copy the role ARN and external ID → paste into Lumos → click Connect.
Option B: Terraform
data "aws_iam_policy" "AWSSSODirectoryAdministrator" {
arn = "arn:aws:iam::aws:policy/AWSSSODirectoryAdministrator"
}
data "aws_iam_policy" "AWSSSOMasterAccountAdministrator" {
arn = "arn:aws:iam::aws:policy/AWSSSOMasterAccountAdministrator"
}
resource "aws_iam_role" "lumos_identity_center_role" {
name = "LumosIdentityCenterIntegrationRole"
max_session_duration = 43200
assume_role_policy = jsonencode({
Version = "2012-10-17",
Statement = [{
Action = "sts:AssumeRole",
Effect = "Allow",
Principal = {
AWS = "arn:aws:iam::349123981986:user/global-service-account"
},
Condition = {
StringEquals = {
"sts:ExternalId" = "CHOOSE_YOUR_EXTERNAL_ID"
}
}
}]
})
}
resource "aws_iam_role_policy_attachment" "directory_admin" {
role = aws_iam_role.lumos_identity_center_role.name
policy_arn = data.aws_iam_policy.AWSSSODirectoryAdministrator.arn
}
resource "aws_iam_role_policy_attachment" "master_admin" {
role = aws_iam_role.lumos_identity_center_role.name
policy_arn = data.aws_iam_policy.AWSSSOMasterAccountAdministrator.arn
}